Norton Ghost 12 Dos Versions
Contents • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • History [ ] Binary Research developed Ghost in, New Zealand. After the Symantec acquisition, a few functions (such as translation into other languages) were moved elsewhere, but the main development remained in Auckland until October 2009 at which time much was moved to India. [ ] Technologies developed by 20/20 Software were integrated into Ghost after their acquisition by Symantec in April 2000. Ghost 3.1 [ ] The first versions of Ghost supported only the cloning of entire disks.
However, version 3.1, released in 1997 supports cloning individual. Ghost could clone a disk or partition to another disk or partition or to an image file. Ghost allows for writing a clone or image to a second disk in the same machine, another machine linked by a parallel or network cable, a network drive, or to a tape drive.
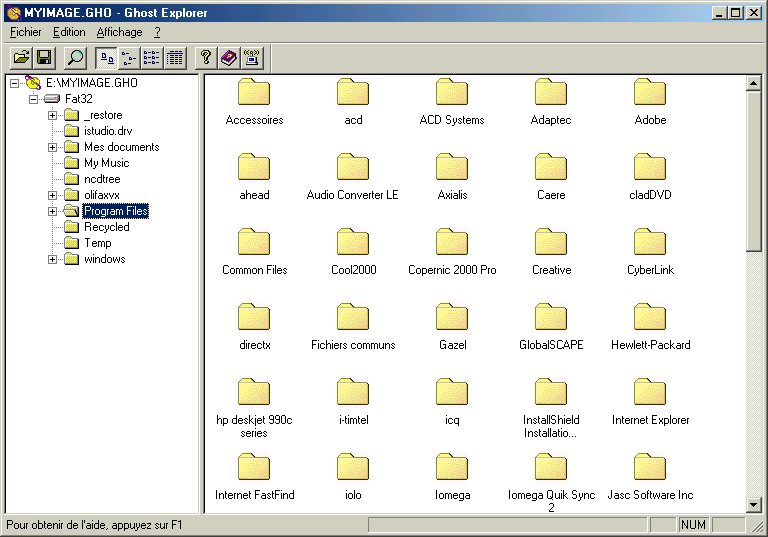
Ghost 4.0 and 4.1 [ ] Version 4.0 of Ghost added technology, following the lead of a competitor,. Multicasting supports sending a single image simultaneously to other machines without putting greater stress on the network than by sending an image to a single machine. This version also introduced Ghost Explorer, a program which supports browsing the contents of an image file and extract individual files from it. Explorer was subsequently enhanced to support adding and deleting files in an image with, and later with,. Until 2007, Ghost Explorer could not edit NTFS images. Ghost Explorer could work with images from older versions but only slowly; version 4 images contain indexes to find files rapidly.
Norton Ghost 12 Dos Version Command. Gho (Ghost) image to. In many Unix shells there is a limit to the number of arguments allowed on a single command. I created a DOS boot diskette, copied ghost.exe from the CD-ROM, and began testing Ghost's cloning feature on four NT 4.0 systems, two running Service Pack 4 (SP4) and two running SP5. Norton Ghost 12 Dos Version Command. Gho (Ghost) image to. In many Unix shells there is a limit to the number of arguments allowed on a single command.
Version 4.0 also moved from to. The additional memory available allows Ghost to provide several levels of for images, and to provide the file browser. In 1998, Ghost 4.1 supports password-protected images. Ghost 5.0 (Ghost 2000) [ ] Version 5.0 moved to.
Unlike the of earlier versions, 5.0 uses a (GUI). The Binary Research logo, two stars revolving around each other, plays on the main screen when the program is idle. In 1998, Gdisk, a script-based, was integrated in Ghost. 900 mhz vs 2 4ghz wifi range. Gdisk serves a role similar to, but has greater capabilities. Ghost for NetWare [ ] A Norton Ghost version for (called 2.0), released around 1999, supports partitions (although it runs in, like the others).
Ghost 6.0 (Ghost 2001) [ ] Ghost 6.0, released in 2000, includes a management console for managing large numbers of machines. The console communicates with client software on managed computers and allows a to refresh the disk of a machine remotely. As a DOS-based program, Ghost requires machines running Windows to reboot to DOS to run it.
Ghost 6.0 requires a separate DOS partition when used with the console. Ghost 7.0 / Ghost 2002 [ ] Released March 31, 2001, Norton Ghost version 7.0 (retail) was marketed as Norton Ghost 2002 Personal Edition. Ghost 7.5 [ ] Released December 14, 2001, Ghost 7.5 creates a virtual partition, a DOS partition which actually exists as a file within a normal Windows file system. This significantly eased systems management because the user no longer had to set up their own partition tables. Ghost 7.5 can write images to discs.
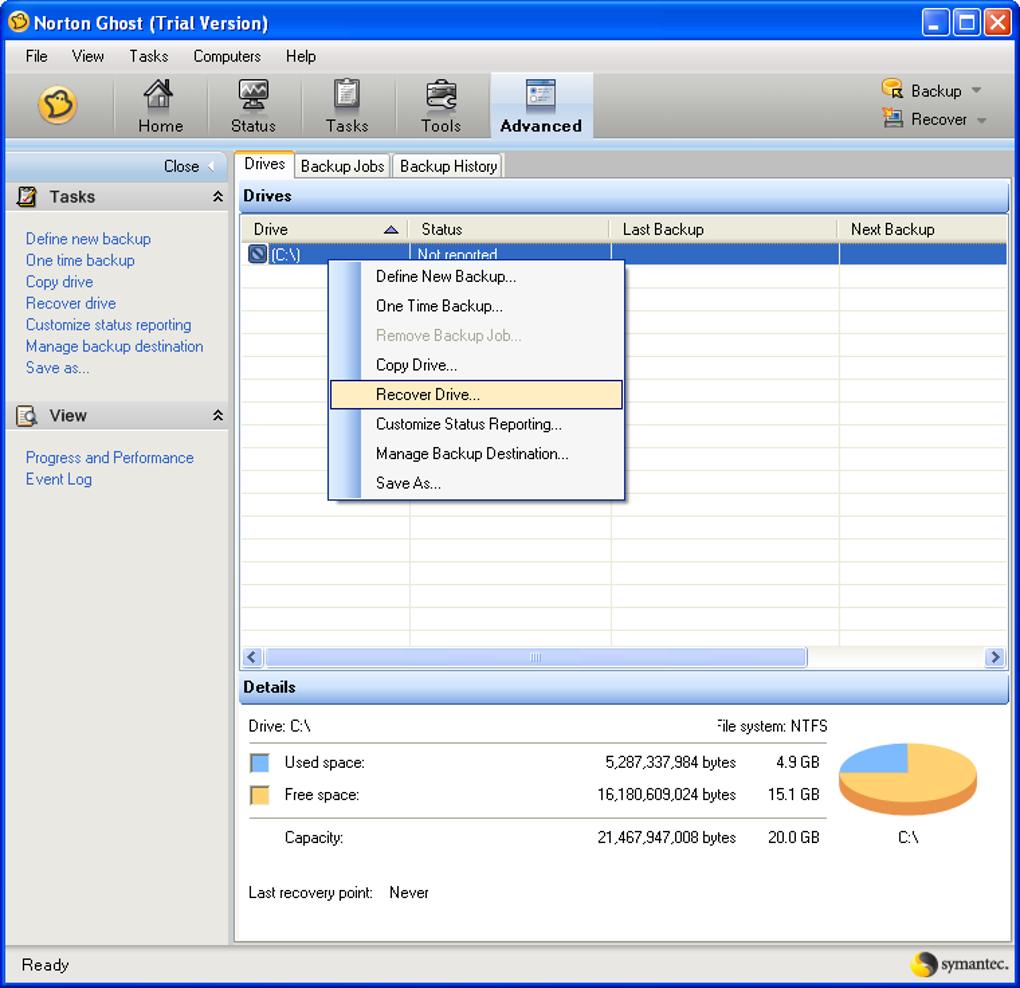
Later versions can write. Symantec Ghost 8.0 [ ] Ghost 8.0 can run directly from Windows. It is well-suited for placement on bootable media, such as ′s bootable CD.
The corporate edition supports, and transfers via. Ghost 8.0 supports NTFS file system, although NTFS is not accessible from a DOS program. Transition from DOS [ ] The off-line version of Ghost, which runs from bootable media in place of the installed operating system, originally faced a number of driver support difficulties due to limitations of the increasingly obsolete 16-bit environment. Driver selection and configuration within DOS was non-trivial from the beginning, and the limited space available on floppy disks made disk cloning of several different disk controllers a difficult task, where different SCSI, USB, and CD-ROM drives were involved. Mouse support was possible but often left out due to the limited space for drivers on a floppy disk. Some devices such as USB often did not work using newer features such as USB 2.0, instead only operating at 1.0 speeds and taking hours to do what should have taken only a few minutes.